Operation Tobacco Road
Operation Tobacco Road
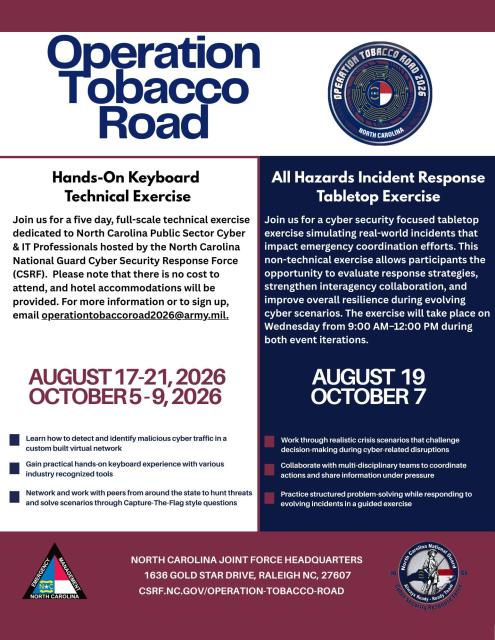
A five-day live-fire cybersecurity exercise designed to simulate real-world enterprise threats and strengthen state cyber readiness.
What to Expect in 2026
Bigger scale, more teams, and a more dynamic environment for returning and first-time participants.
Two iterations
OTR runs twice this year:
August 17—21 and October 5—9
More teams
Each iteration adds two additional teams for deeper operations and cross-team engagement.
Structured progression
Day 1 familiarization → Days 2–5 follow a centralized theme with injects and escalating difficulty.
Built-in learning
Daily “Purple Hour” sessions let Red and Blue teams review tactics and lessons learned.
Operation Tobacco Road 2025:
- Day 1: Range Familiarization, Network Validation, and Tool Validation
- Day 2: Live Red | Blue Team event
- Day 3: Live Red | Blue Team event
- Day 4: Live Red | Blue Team event
- Day 5: Culminating Event and After Action Review
Exercise Overview
Across the board, these exercises serve two major purposes. First, they help to validate existing plans, policies, procedures, and capabilities. Testing how different organizations and agencies at all levels of government and in critical infrastructure sectors will collaborate in response to an emergency verifies that their plans will be effective when a real-world cybersecurity incident arises. Second, these exercises help participants identify resource requirements, capacity constraints, and potential areas for improvement.
The Operation Tobacco Road Exercise currently uses the Persistent Cyber Training Environment (PCTE), a US Cyber Command training environment. The live training environment allows participants to work together in an environment that mirrors the same infrastructure that they see in networks they are responsible for defending on a day-to-day basis.
Operating against teams emulating the tactics and techniques of real-world cyber threat actors, participants test their capability to recognize, identify, and respond to malicious cyber activity.
The scenario runs in a low-stress, no-fault environment where participants are encouraged to collaborate and challenge assumptions.
Operation Tobacco Road is unique in that it moves beyond the theoretical and into the world of the practical, where real-time results and consequences of incident response choices become clear. It isn’t discussion-based like a typical tabletop exercise and instead puts participants on the spot just like they would be in a real cybersecurity scenario. The exercise also fosters relationship building between IT staff, cyber experts, and peer organizations.
The All Hazards Incident Response Tabletop Exercise (TTX) is a discussion-based, non-technical exercise focused on incident coordination, decision-making, and response planning during realistic cyber-related disruptions.
Unlike the hands-on keyboard portion of Operation Tobacco Road, the TTX allows participants to work through response actions, communication flow, and leadership decisions in a guided environment.
The TTX is intended for personnel involved in leadership, coordination, and incident response decision-making.
- Executive leadership
- Managers and supervisors
- Emergency management personnel
- Incident response coordinators
- IT and cybersecurity leadership
- Operational and program decision-makers
It is especially useful for organizations that want to strengthen cross-team coordination and better understand how technical incidents can affect business operations and emergency response efforts.
Provides exercise support to the Blue Teams during the exercise to include technical and non-technical guidance.
Roles
- Lead Controller (LC): Provides timely and efficient management of the exercise. Provides troubleshooting assistance.
- Observer Controller (OC): Embedded with Red Team. Subject matter experts on Blue Team training objectives. Works directly with TO to control the flow of scenario events to the Blue Teams.
- Technical Observer (TO): Embedded with Blue Team. Observation and documentation. Responsible for evaluating and documenting Blue Team actions.
Blue Team Organization
- What is a Blue Team?: Defensive security professionals responsible for maintaining internal network defenses against cyber-attacks and threats.
Who is eligible to participate? IT professionals of all skill levels from North Carolina State, Tribal, Local Government, including K-12 Schools, Critical Infrastructure, UNC System, or the NC Community College System.
If you are interested in participating in Operation Tobacco Road (OTR) or the Tabletop Exercise (TTX), please contact us at operationtobaccoroad2026@army.mil . To ensure availability for all participants, individuals may only participate in one exercise per week.
What tools will be used by the Blue Teams?
- NSM (Zeek)
- Suricata (IDS)
- Elastic
- Kali Linux
- Windows Sysinternals
- PowerShell
- NMAP
- Putty
- BurpSuite - Free Edition
- Flare VM
Feel free to contact us at operationtobaccoroad2026@army.mil for any inquiries.
Operation Tobacco Road 2026:
- Day 1: Range Familiarization, Network Validation, and Tool Validation
- Day 2: Live Red | Blue Team event
- Day 3: Live Red | Blue Team event
- Day 4: Live Red | Blue Team event
- Day 5: Culminating Event and After Action Review







